The collapse of Islamic State’s “caliphate” has had an enormous impact on jihadist activism on the Internet. In a short space of time, we have witnessed a shift from an ecosystem that orbited around the leadership of a strong organisation capable of shouldering the initiative and most of the work needed to ensure the visibility of the jihadist message on Internet, to a different model which is based on a much smaller core and in which the initiative has been taken up by an amalgamation of uncoordinated, small-scale actors who seek to fill the void left by an organisation in retreat.
Grass-roots activists and “media platforms” lacking effective ties to terrorist organisations have acquired an increasingly prominent role in parallel with the “tightening up” of Internet regulation with regard to spreading the messages of radicals. The combination of these two factors has led to the emergence of three trends:
Trend One: New forms of activism driven by the need for continued access to major platforms
As a result of the much more proactive stance adopted by services such as Youtube, Twitter, and Facebook, the jihadist message is finding it increasing difficult to reach its intended audience.[1] The problem is not just the ever-shorter time gap between the publication of radical material and its subsequent removal, with algorithms even able to detect and block illegal content before the publication process is completed. Rather, for the first time ever, the real challenge faced by jihadism is no longer to maintain its presence on the most popular social networks but to actually gain access to them.
The aforementioned companies have gradually introduced tougher registration procedures which make it difficult to create anonymous profiles or generate mass accounts using automated procedures. One of the most common methods is the requirement to provide a mobile telephone number with which interaction is required to verify the user’s identity and complete the registration. Overcoming such hurdles using technical means is becoming increasingly difficult as systems are constantly being improved and made more sophisticated.
The short-term solution the jihadists have adopted is to encourage new forms of collaboration by activists to help circumvent these access issues. Cases have been detected, for example, of activists secretly using the mobiles of friends and family to create new accounts. Similarly, SIM cards have been acquired illegally in massive numbers for the sole purpose of creating new social media profiles, which are then “donated” to the propagandists.[2]
In the same vein, one can assume that a myriad of procedures will be adopted whereby fraud or selective incentives will be used to recruit more and more individuals to the arduous task of guaranteeing access to the major platforms.
Trend Two: The colonisation of small spaces
Cyber-jihadists have been forced to occupy other spaces which do not allow them to reach a mass audience, but nonetheless serve as virtual repositories, meeting points for committed activists, and spaces where private communications can take place more securely.
The smaller the human infrastructure supporting such services, the more likely jihadists are to operate in them relatively trouble-free. The companies in question are generally start-ups, where the idea is to achieve very rapid success with limited financial expenditure.
The start-up model is one where the available resources are geared almost exclusively to providing the service and generating additional revenue, attempting to induce mass-adoption of the product on the Internet before financial paralysis sets in. This means that things like supervising the terms of use or satisfying the constant requests for collaboration by the authorities are viewed as expensive distractions. The undesired side-effect of this philosophy is that the early-adopters of these new Internet products increasingly include supporters of jihadism among their ranks.
Trend Three: The growing prominence of media support networks
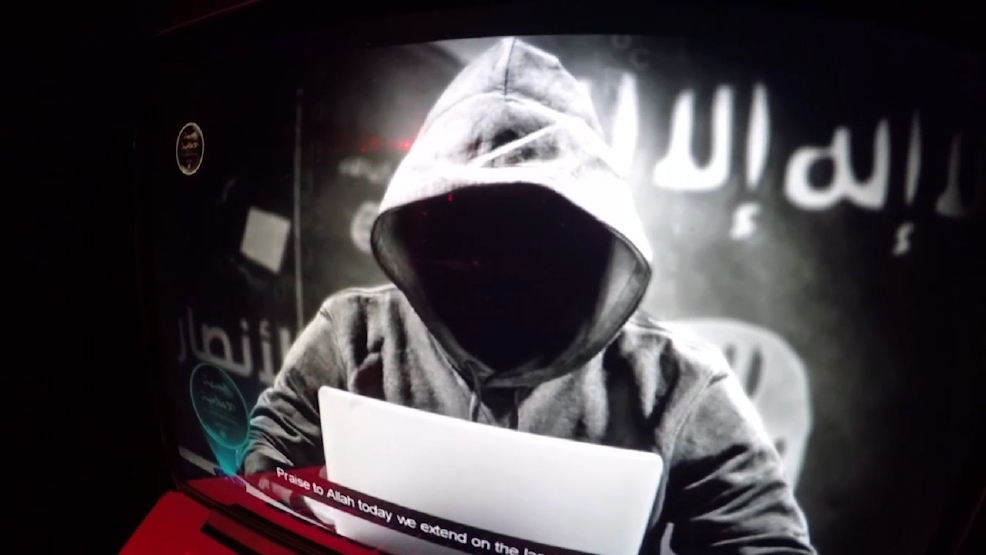
Recent years have seen the proliferation of new names and “media platforms” dedicated to the production and dissemination of self-produced content. These outlets are inspired by directives issued by groups such as Al-Qaeda and the Islamic State, but they are not directly controlled by these groups and their output is of a lower technical quality, tending to consist of reiterations or pastiches of existing propaganda, rather than wholly novel material.
That said, the capacity of these “fanboy” outlets to attract the attention of the Western media is considerable, vastly outweighing the actual threat they represent. Various reasons account for this.
Firstly, the “media platforms” in question show few inhibitions when it comes to publishing unendorsed threats or claiming responsibility for incidents unrelated to terrorism, among them the alarm triggered in Australia by needles concealed in strawberries sold in supermarkets.[3] Quite the opposite: they have advertised in great detail the dates and targets of such attacks in the hope that their calls will spur spontaneous acts of terrorism. The high media impact achieved has been facilitated by the ignorance or sensationalism of certain parts of the press, who have been quick to describe these statements as “messages from Islamic State,” despite the authors having no direct ties to the terrorist group.
Secondly, these actors have demonstrated considerably creativity, as well as an ability to draw lessons from the environment they hope to influence. A prime example is the campaign of threats against the 2018 World Cup in Russia. Following the extensive media coverage generated by the staged photos of footballers depicted as hostages about to be beheaded,[4] the propagandists disseminated a number of different versions of this unexpected propaganda coup. Their hyperactivity ended up backfiring: by saturating the information space with such content, the media soon concluded that its appearance was no longer newsworthy.
While Islamic State has spent months attempting to rationalise for its audience an avalanche of bad news arising out of the collapse of its statelet in Iraq and Syria, and struggling to keep its media operations alive, the aforementioned platforms enjoy easy access to public opinion. Established organisations need to protect their reputation and cannot compromise their credibility with specific promises of an attack which they know they will be unable to carry out. By contrast, these “unofficial” platforms can create immediate media impact with an empty threat — that in turn gives attention to the Islamic State. When one “unofficial” brand is discredited, it can be quickly replaced by a new one that exploits the same ambiguity about its ties to the terrorists’ command structure and individuals willing to perpetrate an attack to generate attention.
There are diminishing returns to these practices, however. Although initially, actions of this nature were useful to enable jihadism to offset, in the minds of the faithful at least, the setbacks suffered on the ground, over the medium term these media support networks have damaged the Islamic State’s credibility, since it was evident that these groups — though independent — had some level of sign-off from the Islamic State. As this dynamic set in, it prompted the Islamic State to distance itself publicly through a communiqué, warning its followers to only heed messages distributed via “official” channels.[5]
All the above has led to the paradoxical situation today whereby the propaganda actions, respectively, of jihadist organisations and those of the networks of their Internet supporters have become differentiated spaces that not only compete with each other for the same audience but also damage each other mutually, even though they pursue the same goal.
References
[1] CONWAY, Maura; KHAWAJA, Moign; LAKHANI, Suraj; REFFIN, Jeremy; ROBERTSON, Andrew & WEIR, David. “Disrupting Daesh: Measuring Takedown of Online Terrorist Material and its Impacts”, Policy Report VOX-Pol (2017).
[2] CASCIANI, Dominic. “Islamic State ‘Sim card man’ jailed”, BBC News, 27 April 2017.
[3] AFP. “’Food terrorism’: Australian strawberry scare continues as more needles found in fruit in copycat attacks”, The Journal, 18 September 2018.
[4] BAKER, Neal. “ISIS releases sick poster of Lionel Messi crying blood in captivity in chilling Russia World Cup 2018 threat”, The Sun, 24 October 2017.
[5] ESISC. “Islamic State reconsiders its online propaganda strategy in a bid to distance further from pro-IS media accounts and to better target western audience”, 28 September 2018.
Dr. Manuel R. Torres Soriano is an Associate Professor of Political Science at Pablo de Olavide University of Sevilla (Spain) and Director of the Diploma in Analysis on Jihadist Terrorism, Insurgencies and Radical Movements of this university. You can follow him on Twitter:@mrtorsor
This article was originally posted on European Eye on Radicalization website. Republished here with permission.