By Laurence Bindner
This post was originally published on our Blog in French in January 2019. It was cross-posted with permission from Ultima Ratio, IFRI’s security and defence Blog. This is its first time appearing in English. [Ed.]
The appeal trial of the administrators of the Ansar al-Haqq forum got under way at the Paris Regional Court (Tribunal de Grande Instance de Paris) on Monday (20 May, 2019). The following post was written in the wake of the initial trial that was held in July 2018.
The four defendants (David Ramassamy, Nordine Zaggi, Farouk ben Abbes and Léonard Lopez – the latter held by Kurdish forces in a Syrian camp) were moderators and administrators of the website between 2006 and 2010. Eight years later the trial is of importance as Ansar al-Haqq remains one of the premier ‘historic’ reference French-language websites linked to the jihadist movement.
The aim of the following piece is to make a brief synthesis of the key questions that have arisen during the trial on the issues of online jihad: What was the precise role of these cyber-activists? How should one assess the reach of their influence, between transmission of the dogma, popularization of the ideology, and information sharing on the one side, and the operational use of the internet to support jihad, the incentive to take part in it or to carry out an attack on the other side? The stake for the parties was the qualification of facts, between glorification of terrorism and terrorist conspiracy.
The Court ruled for the terrorist conspiracy and sentenced the defendants to 3 to 5 years of imprisonment. In addition, F. Ben Abbes was sentenced to permanent exclusion from French territory.
The Court’s decision in favour of the terrorist conspiracy qualification was established around the following themes:
The Operational Use of the Forum
Several elements that substantiate possible operational use of the forum were mentioned during the hearings; these included the release by one of the defendants of a Taleb’s phone number, the sharing of an online encryption tool, and the translation of the summary of a handbook on jihad. The defence showcased the “information” value of those elements, and their lack of consequences; in particular, the encryption tool had neither been downloaded nor viewed. The question of intentionality, as opposed to unintended consequences, was raised by the prosecution – to what purpose, if not to encourage, incite, recruit, were these elements shared online?
The issue of the operational use of the internet for terrorist purposes is all the more crucial as this utilisation has been expanding ever since, with the now widespread employment of encrypted messaging apps. For instance, Telegram, due to its aggregating the functionalities of host, social media, and encrypted messaging application is a platform of choice to replicate some support functions of jihad in the digital space. This is true both from an offensive perspective (i.e. in making handbooks and tutorials available, in sharing fundraising campaigns, etc.) and from a defensive one, with the widespread and systematic sharing of anonymisation tools, thus facilitating browsing, payment, communication, etc.
The Dogma as a Stepping Stone Towards Violent Action?
Where should the line be drawn between dogma dissemination, the exegesis of jihadist ideology, and the call for jihad? According to one of the defendants, al-Qaeda’s ideological line should not be correlated with its “military action” (sic). Can the sharing or translation of ideological texts such as those of Abu Muhammad al-Maqdisi, one of the most influential clerics and theorists in the jihadist intellectual sphere, likely reinforce radicalisation, perhaps even generate it, and prompt an individual towards violent action? In the first place, these questions involve media activists themselves, for whom the permeability between digital and real jihad was substantiated. Léonard Lopez, one of the defendants, had indeed decided to emigrate to Syria before joining ISIS. This permeability showcases the blurry boundary that may exist between digital activism and operational commitment: the close link between propaganda and operations as part of a whole is indeed materialised at the highest level of jihadist groups—be it ISIS or al-Qaeda—that incorporate their media branches within the command leadership.
The « Grey Area » between Information, Indoctrination and Support
From the “mere translation” of communiqués to “releasing communiqués without comment nor apology” was one of the defendants’ shared defence arguments, aiming to highlight the informational purpose of Ansar al-Haqq. On the other hand, the prosecution showcased its prolific, systematic activity, including numerous shares, messages, translations, and monolithic bias, given only information on the Jihadist movement was being shared and de facto legitimised, since other schools of thoughts were not represented. The reference made by one of the defendants to this “information and indoctrination” purpose sheds light on the porous boundaries between information and support in some editorial contexts, an ambiguity currently spreading to various platforms.
The prosecution argued that translating content and making it available to non-Arabic nor English-speaking audiences was a way of promoting this content to French-speaking audiences, so that they could apprehend it and familiarise themselves with its rhetoric.
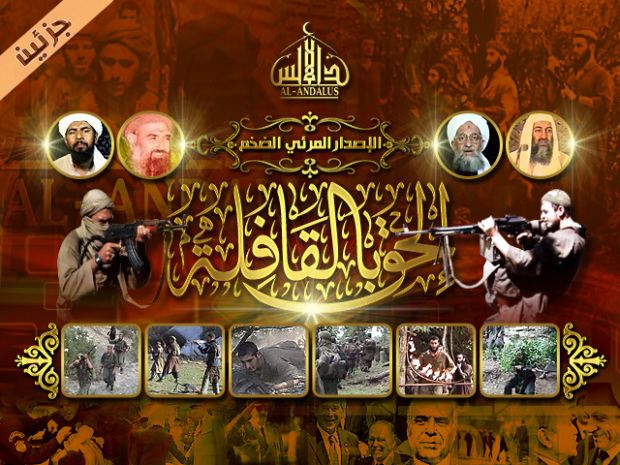
Affiliation
The forum’s neutrality was questioned by its affiliation to a terrorist group. Ansar al Haqq’s affiliation to the GIMF (Global Islamic Media Front – a media consortium relaying al-Qaeda content) appears to have been considered, but nevertheless not completed. This potential affiliation raises the subsidiary question of the complex media ecosystem linked to a specific terror group and the continuum between core media of this group, affiliated outlets, supporter media, and groups or individuals a more neutral stance sharing content.
The Platform’s Positioning as a Mere Host
One of the defendants claimed to hold “a principled position against terrorism,” but acknowledged “infiltrations” in some sections of the forum of members who wrote apologetic posts. That positioning of the forum (host vs. content publisher) raises the topical issue of platforms’ liability for the content they host, particularly social media platforms where this content go viral. Should the task of defining a perimeter around acceptable or licit content fall on these platforms and the private sector, or is it a state prerogative?
The Importance of Digital Evidences
Some elements of the case relied on digital evidence, including the number and frequency of messages, identification of their authors, and evidence of file deletion. This digital evidences has become harder to obtain over the last number of years due to the broader use of encrypted messaging applications and secure email services, along with growing awareness of anonymity and privacy tactics and tools. Currently prominent are issues of (non-)cooperation between the private sector (i.e. operators or platforms who hold evidence) and the authorities.
By ruling in favour of the terrorist criminal conspiracy, the Court acknowledged the impact that media jihad may trigger. Notwithstanding the migration of media jihad from websites and forums to social media and encrypted messaging applications as the main dissemination channels, the issues mentioned above remain topical. Beyond the influence of jihadist content consumption, a range of functions supporting jihad has been transposed into the digital world during the past few years, thus leveraging a “connected jihad”, both for recurrent needs (e.g. funding, anonymization tactics, etc.) and/or more operational ones (e.g. scouting of targets, purchase of weapons, livestreaming of attacks, etc).
Of course, remote-controlled terrorism, that involves only online links between the perpetrator(s) of an attack and its planner(s), is a more advanced type of virtualisation of terrorist action, which has already occurred.
Laurence Bindner is the co-founder of JOS Project, and Alexander Stonor, analyst at JOS Project. You can follow her on Twitter: @LoBindner