Blog
Blog
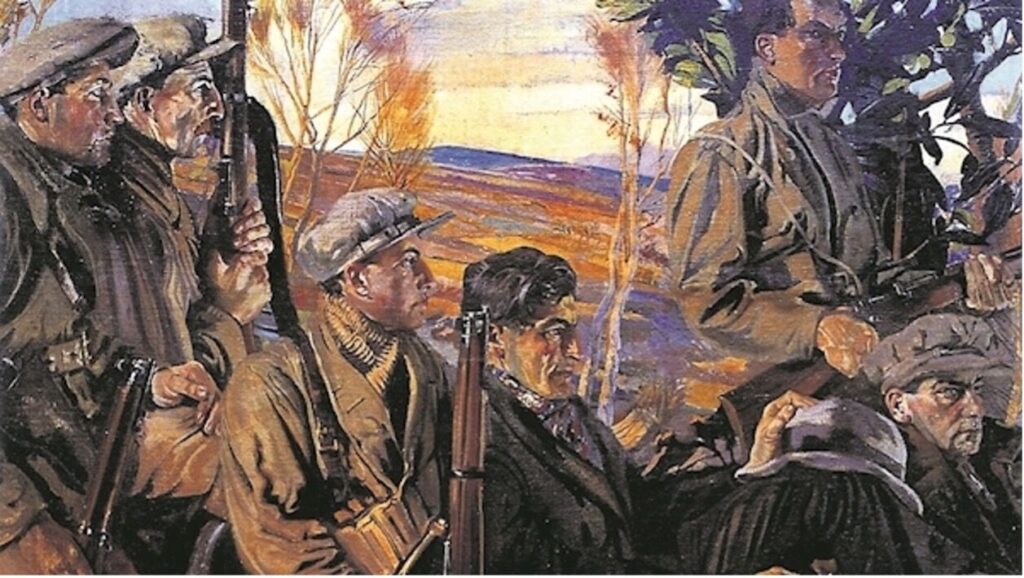
Masculinity and Militant Traditions: The Shaping of a Home-Grown Irish Far-Right
February 11, 2026By Joshua Farrell-Molloy Only a decade ago, Ireland’s far right was barely visible. Its current form is rooted in 1990s anti-abortion activism, which shaped the political careers of figures Justin Barrett and James Reynolds, who in 2016 co-founded the National Party, Ireland’s largest far-right party. The 2018 abortion referendum provided an early incubation space for ...
Blog
AI, Anger and Entitlement: What’s Fuelling Misogynistic Extremism Online
February 4, 2026By Bernadette Johnston Misogyny and problematic attitudes towards women are not new phenomena. What is new however is the speed and scale at which misogynistic ideas and related behaviours now circulate – particularly online. Problematic ‘nudification apps,’ whose sole purpose is to underdress and sexually transform photos of women online without their consent, have existed ...
Blog
Online Terrorist Exploitation: Responding to Children as Victims and Perpetrators
January 28, 2026By Gina Vale In December 2021, terrorism charges against a 14-year-old British girl were dropped—not due to lack of engagement with extremist networks, but on account of the power dynamics of her digital relationships therein. The Home Office Single Competent Authority (SCA) determined that she was a victim of modern slavery in the UK for ...
Blog
Far-right extremists have been organizing online since before the internet – and AI is their next frontier
January 21, 2026Michelle Lynn Kahn, University of Richmond How can society police the global spread of online far-right extremism while still protecting free speech? That’s a question policymakers and watchdog organizations confronted as early as the 1980s and ’90s – and it hasn’t gone away. Decades before artificial intelligence, Telegram and white nationalist Nick Fuentes’ livestreams, far-right ...
Blog
Bondi attack came after huge increase in online antisemitism: research
January 14, 2026By Matteo Vergani, Deakin University At least 16 people – including a ten-year-old child – are dead after two men opened fire on a crowd of people celebrating the Jewish holiday of Hanukkah on Sunday in a public park at Sydney’s Bondi Beach. Many more are injured. I am horrified. But as a researcher who ...
Blog
Misogyny as an Operational Strategy in India’s Digital Extremism
January 7, 2026By Antara Chakraborthy On the 19th of December 2024, Atul Subhash, a 28-year-old techie from Bangalore, India, recorded an 80-minute video blaming his wife, feminism, and the Indian court system, before ending his life. Within hours, his video and suicide note were widely circulated by India’s men’s rights organisations in India. Subash was hailed as ...
Blog
Visits to Gore Sites Driven by Searches for Graphic Footage of Charlie Kirk’s Death
December 31, 2025By Human Digital Introduction Across the 10th and 11th September 2025, people seeking footage of the shooting of Charlie Kirk triggered a 110% increase in total visitor numbers to 21 gore sites (Figure 1). As detailed in Human Digital’s VOX-Pol report, Gore & Violent Extremism, those visitors will have been exposed to videos involving graphic ...
Blog
The Latest Far-Right Rift: Rejecting ‘Third Worldism’
December 24, 2025By Kye Allen Introduction On 3 July, Constantin von Hoffmeister, then editor-in-chief of Arktos—the leading publisher of Eurasian, identitarian, and New Right thought—announced a new venture, Multipolar Press. Within two months, he was removed from his editorial position at Arktos. Unpacking the reasons behind his dismissal reveals ideological fissures within the far right’s intellectual milieu. ...
Blog
Highlights from the 2nd Annual Workshop of the Canadian Network for Research on Security, Extremism and Society
December 17, 2025By Garth Davies and Mackenzie B. Hart On September 25 and 26th, the Canadian Network for Research on Security, Extremism and Society (CANSES) hosted its 2nd Annual Workshop at Saint Mary’s University in Halifax, Nova Scotia. First and foremost, CANSES is a network that connects individuals working on extremism across a variety of sectors. Reflecting ...
Blog
The Human Cost of Countering Violent Extremism with Youth: The Importance of Reflective and Supportive Practice
December 10, 2025By Sarah Stevenson and Dr Steve Barracosa Practitioners working in the field of countering violent extremism (CVE) are routinely exposed to confronting and offensive ideas and content, including graphic violence, gore, hate, terrorist propaganda and ideologies. Despite this, there is a relative gap in the literature considering the experiences and well-being of practitioners undertaking this ...